parameters from Internet Explorer 5+ and Firefox 3+ by using IE/Firefox tamper tool. Since the tool exposes and
allows tampering with inconvenient input, It can help user to detect user-input security flaws (e.g. XSS and SQL
injection vulnerabilities).
WARNING: This tool makes it simple to carry out malicious attacks against poorly-written code. Such willful use
of this tool against third-parties is a violation of federal, state, and local laws.
Important Request Builder features include:
| · | Works with secure HTTPS connections.
|
| · | Modifying HTTP request headers.
|
| · | Modifying IE/Firefox Cookie.
|
| · | Build or Modify Query Strings.
|
| · | Build or Modify POST form-urlencoded data or other raw (e.g. xml) data.
|
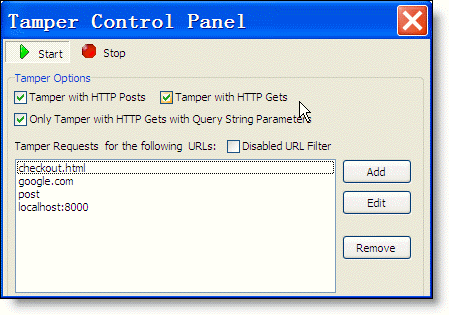
Tamper IE/Firefox Control Panel
Click "Tools->Tamper IE/Firefox..." will show the following control panel and ready to tamper IE/Firefox Http Requests. The Control Panel allows you to control when you are prompted to tamper with requests.
|
Control
|
Function
|
|
Start
|
Enable Tamper IE/Firefox Requests.
|
|
Stop
|
Disable Tamper IE/Firefox Requests.
|
|
Tamper with HTTP POSTs
|
Show the Tamper editor dialog when a form is submitted with METHOD=POST
|
|
Tamper with HTTP GETs
|
Show the Tamper editor dialog whenever a HTTP GET is performed.
|
|
Only tamper with GETs with Query string parameters
|
Show the Tamper editor dialog only when a HTTP GET is performed and there is query string data in the URL. Query string data is found in the URL after the ? character. For instance, in this Google hit, query data is shown in Red.http://www.google.com/search?hl=en&q=httpanalyzer
|
|
Tamper requests for the following URLs
|
Show the Tamper editor dialog whenever a HTTP GET is performed and the resource address contains with the specified text.
For instance, given the filter in the above screenshot, the following URL requests will match: www.onlineby.com/checkout.html http://www.google.com/search?hl=en&q=httpanalyzer http://www.ieinspector.com/test/testpost.htm etc... |
|
Disabled URL Filter
|
Disable/Enabled the URL filter function, all GET/Post requests will match the filter.
|
When the tamper control panel is shown and the "start" button is down, If the browser navigates an URL which matches with tamper filter, the Tamper IE/Firefox request editor of tamper dialog is shown.
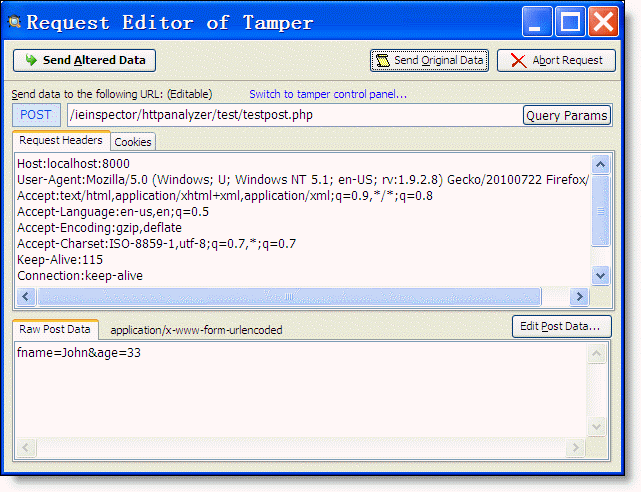
When the method is "POST", you can click the "Edit post data..." to show the "POST Data Editor" dialog and modify the post data.
POST Data Editor Dialog
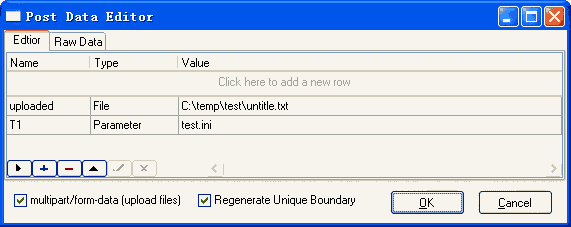
| · | Multipart/form-data (upload files): Determines whether using multi part/form-data POST method to upload files via HTTP protocol.
|
| · | Regenerate Unique Boundary: Determines whether regenerating unique boundary when posting multi part/form-data.
|
When confirming the changes by clicking the OK button, the headers "Content-Type" and "Content-Length" is auto recalculated and added to the request headers.
Query String Editor Dialog
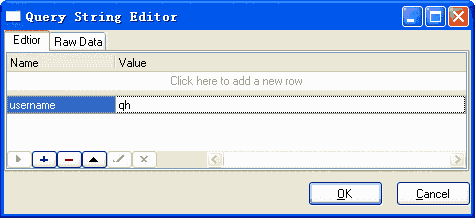
The Query String Editor allows you to add or modify the query string.